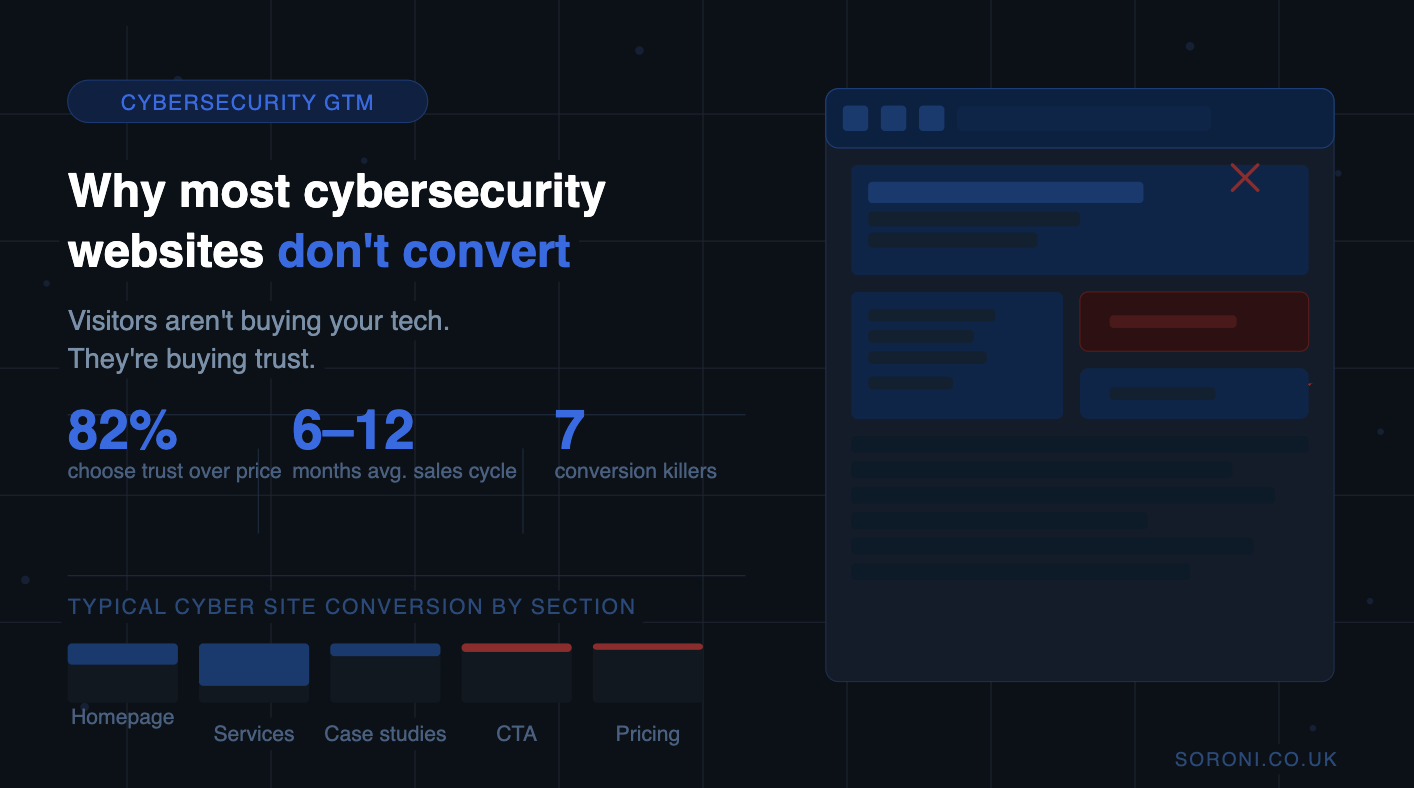
Why Most Cybersecurity Websites Fail to Convert
Your prospects aren’t buying your technology. They’re buying trust. And most cybersecurity websites are accidentally destroying it.
A cybersecurity vendor can have best-in-class technology, a strong sales team, and a healthy events calendar — and still watch qualified prospects land on their website and leave without converting. This isn’t a traffic problem. It’s a trust problem. And the website is where trust is won or lost.
Here’s the uncomfortable truth: most cybersecurity websites were built to impress peers, not to convert buyers. They lead with architecture diagrams, feature matrices, and threat intelligence language that means everything to an internal team and almost nothing to the CFO who just signed off on the budget.
Understanding why this happens — and how to fix it — is the difference between a website that generates pipeline and one that merely exists.

The core problem: feature-led, not outcome-led
Most cybersecurity websites speak fluent technology. They describe what the product does — detection capabilities, integration depth, response times, compliance coverage. What they rarely communicate is what changes for the buyer as a result of choosing you.
This matters enormously because security buying decisions are not purely rational. They are risk-transfer decisions. The CISO is asking: “If something goes wrong after I buy this, can I defend this decision to the board?” The CFO is asking: “Is this spend protecting something of real commercial value?” The procurement lead is asking: “Is this vendor credible enough to trust with our infrastructure?”
None of those questions are answered by a feature list. They’re answered by trust signals — evidence, outcomes, credibility, clarity of value.
A website that leads with technical capability assumes the visitor already trusts you enough to read the detail. In reality, trust must come first.
The seven conversion killers
These are the most common — and most costly — mistakes we see on cybersecurity websites.
1. Jargon-first messaging that alienates buyers
Terms like “zero-day threat intelligence”, “SIEM-native ingestion”, and “lateral movement detection” mean something to a SOC analyst. To the financial director co-signing the purchase order, they signal complexity, not confidence.
Your homepage needs to answer one question clearly within five seconds: what does this company protect, and who does it protect it for? If a non-technical executive can’t answer that question after reading your hero section, you’ve already lost half your buying committee.
❌ “AI-powered adaptive threat intelligence platform”
✓ “We help financial services firms prevent the breaches that damage trust”
Security buyers are deeply sceptical. They’ve been burned by vendor overpromising. They have seen breach reports from vendors claiming to be secure. They need evidence before they’ll engage — and most cybersecurity websites either offer none, or offer the kind that doesn’t land with buying committees.
A generic testimonial from a technical user carries far less weight than a named case study showing a measurable outcome for a recognisable organisation type. Board-level buyers want to see: who else like us has trusted you, what happened, and what was the measurable result.
❌ “Trusted by 500+ companies worldwide”
✓ Named case study: 40% reduction in incident response time for a regulated financial services firm
A cybersecurity purchase involves a CISO, a CTO, a CFO, procurement, and often a board sponsor. Each of these people has fundamentally different concerns, language, and buying criteria. A homepage that tries to speak to all of them simultaneously ends up connecting with none of them.
The most effective cybersecurity websites either lead with a clear primary persona, or build deliberate pathways for each audience type — separate landing pages, audience-specific messaging tracks, or clear navigation that says “I’m a CISO” vs “I’m evaluating on behalf of my board”. Segment early. Convert faster.
2. No proof, or the wrong kind of proof
The default CTA on most cybersecurity websites is “Request a Demo” or “Get in Touch”. The problem is that neither of these is appropriate for a buyer who is in early-stage research — which describes the majority of inbound traffic.
Security buyers don’t want to speak to sales until they’ve built internal confidence in a vendor. Pushing a demo too early triggers avoidance. Effective CTAs match the buyer’s stage: a buyer exploring options needs a guide, a framework, or a benchmark tool — not a sales call.
❌ “Book a demo” as the only CTA✓ “Download: The CISO’s Guide to Evaluating Identity Security Vendors”
3. One message trying to serve multiple audiences
A cybersecurity purchase involves a CISO, a CTO, a CFO, procurement, and often a board sponsor. Each of these people has fundamentally different concerns, language, and buying criteria. A homepage that tries to speak to all of them simultaneously ends up connecting with none of them.
The most effective cybersecurity websites either lead with a clear primary persona, or build deliberate pathways for each audience type — separate landing pages, audience-specific messaging tracks, or clear navigation that says “I’m a CISO” vs “I’m evaluating on behalf of my board”. Segment early. Convert faster.
4. Weak or misaligned calls to action
The default CTA on most cybersecurity websites is “Request a Demo” or “Get in Touch”. The problem is that neither of these is appropriate for a buyer who is in early-stage research — which describes the majority of inbound traffic.
Security buyers don’t want to speak to sales until they’ve built internal confidence in a vendor. Pushing a demo too early triggers avoidance. Effective CTAs match the buyer’s stage: a buyer exploring options needs a guide, a framework, or a benchmark tool — not a sales call.
❌ “Book a demo” as the only CTA
✓ “Download: The CISO’s Guide to Evaluating Identity Security Vendors”
5. No commercial clarity — the “what does this actually cost” problem
Cybersecurity vendors are notoriously reluctant to provide any pricing context on their websites. This is understandable — enterprise deals are complex and highly variable. But completely absent pricing information creates a specific problem: it signals to budget-conscious buyers that your product is probably too expensive.
You don’t need to publish a price list. But you do need to give buyers enough context to self-qualify. A pricing page that explains how you charge, what variables affect cost, and what a typical engagement includes removes one of the key friction points in the early buying journey.
6. Missing compliance and regulatory alignment
In 2026, regulatory pressure is one of the most powerful buying triggers in cybersecurity. NIS2, ISO 27001, Cyber Essentials, AI Act compliance — these are no longer nice-to-haves. They are the primary reason many organisations are evaluating security vendors right now.
If your website doesn’t explicitly connect your capability to these compliance frameworks, you are invisible to a significant portion of your addressable market. Regulatory-driven buyers are searching for vendors who speak their language. If your website doesn’t surface compliance alignment prominently, you will not rank, and you will not convert.
7. Treating the website as a brochure, not a conversion system
Perhaps the most fundamental mistake: thinking of the website as a static place to describe what you do, rather than a dynamic system designed to move buyers through a journey.
A cybersecurity website that converts has deliberate architecture. It maps content to buyer stages. It captures intent early with low-friction offers. It nurtures visitors who aren’t ready to buy yet. It uses personalisation and segmentation to serve relevant content to different audiences. It integrates with CRM so the sales team can follow up intelligently. Most cybersecurity websites do none of this.
What a high-converting cybersecurity website looks like
The security vendors who consistently generate inbound pipeline from their websites share a common architecture. It’s not about design trends or the latest UX patterns — it’s about trust, clarity, and conversion logic.
Lead with outcomes, not architecture
Your hero section should communicate the transformation you deliver for a specific type of buyer. Not “AI-powered threat detection” but “We help mid-market financial services firms meet NIS2 requirements without doubling their security headcount.” The specificity is deliberate — it filters in the right buyers and filters out everyone else.
Build a trust stack above the fold
Within the first scroll, a buyer should see: recognisable client logos, a quantified outcome or two, relevant certifications, and evidence that you’ve worked with organisations like theirs. This is the trust stack — and it’s the difference between a visitor reading further or bouncing.
Create audience-specific pathways
Design distinct entry points for the CISO, the CFO, and the compliance or procurement lead. Each pathway should speak to their specific concerns, language, and success criteria. A CISO wants to understand your detection methodology. A CFO wants to understand ROI and total cost of ownership. A compliance officer wants to see certification coverage and audit support.
Offer value before requesting commitment
The buyers most likely to become your best clients are the ones doing thorough research. Give them something valuable before asking for their time — a framework, a benchmark, a guide to the buying decision they’re facing. This builds reciprocity and positions you as a trusted advisor before the sales conversation begins.
Connect your website to your CRM
Every interaction on your website — which pages were visited, which content was downloaded, what was read — is intent data. If that data isn’t flowing into your CRM and shaping how your sales team follows up, you’re generating heat and losing it. HubSpot and Salesforce, properly configured for cybersecurity sales cycles, turn website behaviour into a pipeline signal.
The highest-converting cybersecurity websites don’t just describe capability. They architect a buying journey that earns trust, demonstrates expertise, and moves qualified buyers progressively closer to a conversation.
A conversion readiness checklist
Before your next campaign drives traffic to your website, audit it against these fundamentals:
- Your hero section communicates what you do, for whom, and what changes — without jargon — in under 10 seconds
- Your homepage has at least one named case study with a measurable outcome
- You have distinct messaging or pathways for technical buyers (CISO/CTO) and commercial buyers (CFO/board)
- You offer at least one mid-funnel CTA that provides value before requesting a sales conversation
- Your website references the compliance frameworks your buyers are currently being pressured to meet
- Your pricing page (or equivalent) gives enough context for buyers to self-qualify
- Website behaviour data is flowing into your CRM and available to your sales team before they make contact
- Your trust signals (logos, case studies, certifications) are visible without scrolling past the hero
The bottom line
Cybersecurity is a high-stakes, high-trust category. Buyers are making decisions that carry personal and organisational risk. They are not going to convert on a website that treats them as a technical audience when they are a buying committee.
The good news is that most of your competitors are making the same mistakes. A cybersecurity website that is genuinely built around buyer psychology, trust architecture, and conversion logic is rare — and it shows up immediately in pipeline quality and velocity.
Getting there is a combination of messaging strategy, CRM integration, and content architecture. It’s not a redesign project. It’s a revenue system project.
If your website is generating traffic but not pipeline, the problem isn’t your product. It’s how your website is communicating trust — and that’s entirely fixable.
Is your cybersecurity website built to convert?
We work with cybersecurity companies, MSSPs and SaaS security vendors to build revenue systems that turn technical capability into predictable pipeline. Contact Us →