Cybersecurity Go-To-Market Strategy: How Security Companies Build Predictable Pipeline
Cybersecurity companies don’t struggle because of weak products.
They struggle because of weak go-to-market strategy.
Despite rising global cyber threats, growing regulation, and increasing enterprise security budgets, many cybersecurity vendors still face:
- Inconsistent pipeline
- Long sales cycles
- Founder-led revenue dependence
- Unpredictable growth
The reality is simple:
Pipeline is not a function of demand alone.
Pipeline is a function of how well your go-to-market (GTM) strategy aligns marketing, sales, positioning, and trust.
In today’s enterprise security market, technical capability is no longer enough.
Winning vendors are those that design revenue systems — not just campaigns.
This is where a modern cybersecurity marketing strategy becomes the difference between sporadic wins and scalable growth.
Why Cybersecurity Companies Struggle to Build Predictable Pipeline
Most cybersecurity companies begin with technical excellence.
But technical excellence does not automatically translate into market traction.
Common challenges include:
Founder-Led Selling Dependency
Revenue often relies heavily on founders or senior technical leaders who:
- Understand the product deeply
- Hold industry credibility
- Can articulate value in nuanced ways
This creates growth bottlenecks and limits scalability.
Technical Messaging That Doesn’t Translate
Many vendors communicate in:
- Features
- Architectures
- Detection models
- Encryption layers
But enterprise buyers don’t buy technology.
They buy:
- Risk reduction
- Operational resilience
- Regulatory confidence
Without translating capability into business value, marketing efforts fail to resonate.
Misalignment Between Marketing and Sales
Marketing may generate leads.
Sales may pursue opportunities.
But without shared definitions of:
- ICP
- Qualification criteria
- Buying signals
- Lifecycle stages
Leads don’t convert into pipeline.
Long and Complex Buying Cycles
Cybersecurity decisions often involve:
- CISO
- CIO
- Risk teams
- Procurement
- Finance
- Compliance
Without a structured cybersecurity lead generation and nurturing model, deals stall.
The result?
Plenty of activity — but little predictability.
What a Modern Cybersecurity Go-To-Market Strategy Looks Like
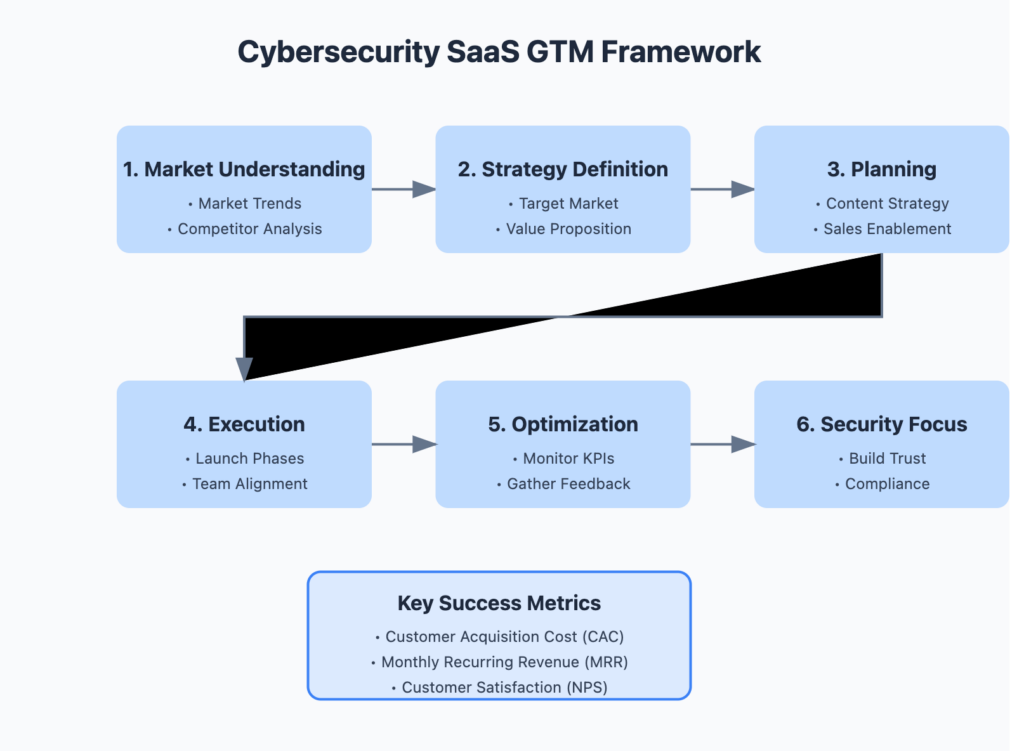
A strong go to market strategy for cybersecurity companies aligns five core pillars:
1. Market Positioning
Security markets are crowded.
To stand out, vendors must move beyond “tool messaging” and define:
- The specific problem they solve
- The business outcome they enable
- The risk they reduce
Effective positioning shifts from:
❌ “We detect threats faster”
to
✅ “We reduce breach exposure in regulated environments”
Outcome-led positioning speaks directly to enterprise priorities.
2. ICP Clarity
Not every organisation is your buyer.
Cybersecurity companies that build predictable pipeline define their Ideal Customer Profile (ICP) precisely.
This often includes:
- Regulated industries (finance, healthcare, government)
- High compliance pressure environments
- Organisations with mature risk management functions
Within those organisations, different stakeholders care about different outcomes:
| Buyer Role | Priority |
|---|---|
| CISO | Risk reduction |
| CIO | Operational continuity |
| CFO | Financial exposure |
| Compliance Lead | Audit readiness |
Understanding these perspectives transforms messaging effectiveness.
3. Buyer Journey Alignment
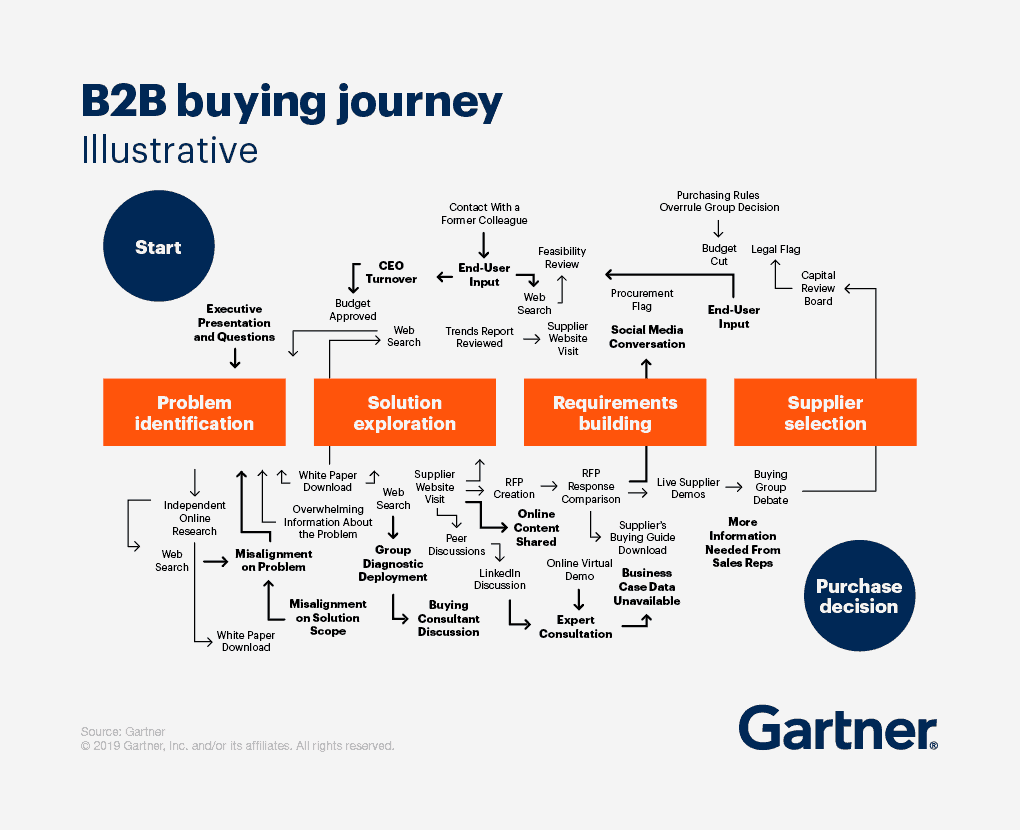
The enterprise cybersecurity buyer journey is not linear.
It typically includes:
- Risk trigger awareness
- Internal alignment
- Vendor exploration
- Trust validation
- Procurement scrutiny
Many marketing strategies fail because they target awareness — but ignore validation and trust.
A successful cybersecurity marketing strategy supports buyers across the full journey.
4. Demand Strategy
Traditional tactics like:
- Generic whitepapers
- One-off webinars
- Gated PDFs
rarely generate high-quality pipeline.
Instead, demand must align to:
- Regulatory drivers
- Industry-specific threats
- Board-level risk conversations
High-performing vendors build campaigns around business impact — not technical novelty.
5. Revenue Infrastructure
Even the strongest messaging fails without operational alignment.
This is where CRM and RevOps become critical.
Without lifecycle clarity:
- Marketing generates interest
- Sales creates activity
- But pipeline remains unpredictable
With structured systems:
- Buying signals are captured
- Qualification improves
- Forecasting becomes reliable
Cybersecurity Lead Generation That Actually Works
Modern cybersecurity lead generation moves beyond volume.
It prioritises intent.
Effective strategies include:
Compliance-Led Campaigns
Campaigns aligned to frameworks such as:
- Zero Trust
- NIST
- ISO standards
resonate strongly with enterprise buyers because they connect directly to governance obligations.
Risk-Based Messaging
Executives respond to:
- Financial exposure
- Operational disruption
- Regulatory penalties
Messaging should frame security as a business risk issue, not just a technical one.
Board-Level Narratives
Security investments are increasingly justified at the executive level.
Content that supports:
- Board discussions
- Strategic planning
- Resilience planning
Accelerates buying decisions.
Building a Predictable Pipeline Model
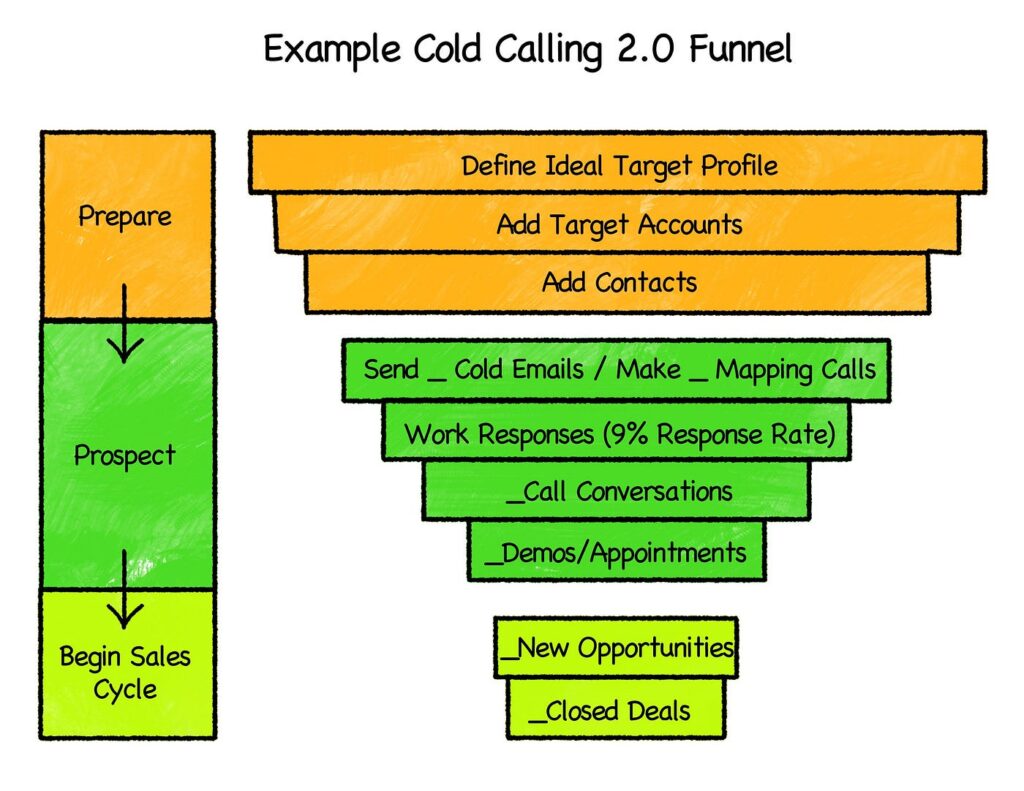
Pipeline predictability does not come from more campaigns.
It comes from better design.
A repeatable cybersecurity GTM model includes three stages:
Step 1: Category Narrative
Define clearly:
“What problem do we uniquely solve?”
This narrative should:
- Anchor messaging
- Align campaigns
- Guide sales conversations
Without it, marketing becomes fragmented.
Step 2: Demand Creation
Demand should map to:
- Regulatory pressure
- Industry-specific risk
- Budget ownership
Effective content includes:
- Executive briefings
- Industry risk insights
- Scenario-based threat discussions
Step 3: Conversion Infrastructure
Conversion depends on operational clarity.
This includes:
- Lifecycle mapping
- Lead qualification logic
- Opportunity stage definitions
- Sales methodologies such as MEDDPICC
Without structured progression, deals stagnate.
The Role of CRM in Cybersecurity Growth
CRM is not just a tracking tool.
It is the foundation of scalable GTM execution.
A well-designed CRM enables:
- Buyer journey visibility
- Pipeline measurement
- Signal detection
- Sales alignment
Without it:
Marketing creates interest.
Sales creates activity.
But growth remains inconsistent.
With aligned systems:
- Marketing understands what converts
- Sales understands what qualifies
- Leadership understands what forecasts
This transforms GTM from guesswork into discipline.
Enterprise Buyers Don’t Buy Features — They Buy Trust
In cybersecurity, trust is the ultimate differentiator.
Enterprise buyers evaluate:
- Vendor credibility
- Framework alignment
- Proven outcomes
- Architecture maturity
Trust accelerators include:
- Industry proof points
- Regulatory alignment
- Transparent implementation approaches
Vendors that position themselves as risk-reduction partners — not just technology providers — win faster.
The Cybersecurity GTM Maturity Model
Cybersecurity companies typically evolve through stages:
| Stage | Description |
|---|---|
| Founder-led selling | Early traction |
| Campaign-led marketing | Initial demand |
| Structured demand engine | Pipeline growth |
| RevOps-led GTM | Predictability |
| Category leadership | Market dominance |
Predictable growth emerges when companies move beyond ad-hoc campaigns into structured revenue systems.
Moving From Leads to Predictable Pipeline
Building consistent pipeline requires alignment across:
- Positioning
- ICP clarity
- Buyer journey understanding
- Demand strategy
- CRM infrastructure
When these elements operate together, pipeline becomes:
- Measurable
- Repeatable
- Forecastable
Final Thought: Cybersecurity GTM Is Now a Revenue Discipline
Cybersecurity is no longer just a technical market.
It is a trust-driven, risk-led enterprise buying environment.
Winning vendors are those that:
- Align marketing to business impact
- Align sales to buying signals
- Align systems to decision journeys
In this landscape, growth is not driven by product alone.
It is driven by go-to-market design.
Want to Build a Predictable Pipeline for Your Cybersecurity Company?
At Soroni, we help cybersecurity companies design and operationalise go-to-market strategies that align marketing, sales and CRM into a single revenue engine.
Because in today’s market, the winners are not just the most secure. They are the most aligned.
Get intouch.

